How to Access a Computer
In this article I will tell you how you can access your computer from the network. Open access to the computer over the network to exchange information with it.
For example, you need to share a folder. Suppose you did this, try to enter this folder from another computer, and you get a window asking you to enter a “username” and “password”, or it gives an error that you do not have enough rights to contact your system administrator.
There are two computers interconnected, and you have a need to share files with each other.
- First computer: it has an ip address 192.168.0.2
- Second computer: it has an ip address 192.168.0.3
- Create a shared folder on the first computer
- Disable Windows Firewall
- Local security policy
- Access your computer from the network
- Deny access to this computer from the network
- Check the performance of this method
- Configuring a local computer-computer network
Create a shared folder on the first computer
Right-click on the desktop, the context menu = create = folder. A “New folder” will appear on the desktop, rename it to “shared”. Right-click on it, the context menu appears = property. Switch to the “Access” tab.
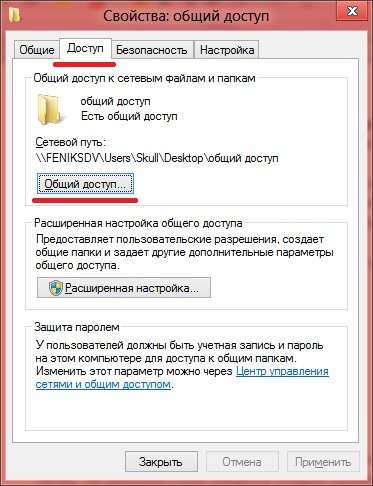
Click on the “Sharing” button, a window appears that looks like this:
In the line where it says “Everything”, you also write this word, then click on the “Add” button. After which you will see the inscription “Everything” below, the value “Read” will be opposite it, click on this word “Read” and select “Read and Write”, and then click on the “Sharing”. “Done” button.
Then you need to click on the “Advanced Settings” button, you will see the following window:
In this window, you need to check the box “Share this folder” and click on the “Permissions” button, after which a new window will appear:
In the column “Allow” you need to put all the checkmarks, and click on the buttons “OK”, “OK”, “Close”. This completes the sharing of the folder.
Disable Windows Firewall
Go to the control panel = administration = Windows Firewall with Advanced Security.
Click on the button “Actions” = “Properties”, a window appears as follows:
On the “Domain Profile” tab there is a “Firewall” item, by default it says “Enable (recommended)”, you select “Disable” and click “OK”. At this point, disabling Windows Firewall is complete.
Local security policy
Configure the “Local Security Policy.” Go to the control panel = administration = local security policy. The following window will appear on your screen:
In this window on the left there are security items “Local Policies” = “Assignment of user rights.” The list of policies opens on the right side, in this paragraph we are interested in two points, in the screenshot they are highlighted in red “Access to the computer from the network” and “Deny access to this computer from the network”.
Access your computer from the network
Double-click on this line, you will see a window like this:
In this window you need to add the “Guest” account, for this, click on the button “Add user or group.”, you will see a new window:
In which you click on the “Advanced” button and go to the following window:
In this window, you click “search”, after which the “search result: in which you should find the” Guest “account will appear, then click on the” OK “,” OK “,” OK “button.
Deny access to this computer from the network
Double-click on this line and you will see the following window:
In this window you need to select the “Guest” account, click on the “Delete” button, and click on the “OK” button. This completes the process of setting up local policies.
Check the performance of this method
We go from another computer, to “my computer”, on the left there will be a column at the bottom, in which there will be a point. “Network”, when you click on it, a window will open on the left where computers of your working group will be indicated. Click on the first computer on which we created the “shared” folder and you should see a window in which this folder is located. Just drag the file into this folder and it will appear on the first computer.
I hope this article has been helpful to you.
What is an Internet-ID?
Internet-ID is the name of the technology with which you can connect to the Host, bypassing firewalls and NAT. To connect to a remote computer, you do not even need to know its network name or IP address. Simply enter its identifier (ID). No additional network equipment settings are also required.
Port forwarding or port mapping is no longer needed to establish a NAT-to-NAT connection.
This functionality is very useful, first of all, to technical support services that work with a large number of clients who do not have the opportunity to provide an external static IP address.
What is the Internet-ID feature for?
The main task that Internet-ID technology solves is to simplify the procedure for connecting to a remote computer as much as possible. Previously, fine-tuning of routers, port forwarding (port forwarding, port mapping) or the configuration of “Reverse connection” were required. All these manipulations are very difficult for ordinary users and sometimes cause problems even for advanced system administrators. Internet-ID avoids all this.
How it works?
Internet-ID technology is based on the fact that a network connection with a remote host is established through special dedicated servers of TektonIT (or corporate Mini Internet-ID server). In turn, the remote host also constantly maintains a connection to these servers.
The principle of operation is very similar to how popular messaging services like ICQ or Skype work.
Configure Internet-ID connection.
In order to be able to connect to a remote Host using an Internet-ID connection, you need to get an identifier on the Host. This automatically activates the Internet-ID mechanism and establishes a connection with our servers.
Right-click on the Host icon, near the system clock. From the menu, select “Configure Internet-ID Connection”.
In the window that appears, click on the “Get a New ID” button.
Remember, write down or copy this identifier to the clipboard. It is useful for access to this Host.
Now the Host is ready to accept connections from the Client (Viewer), access to the computer is configured.
On the Client side, when creating a new connection or in the settings of an existing one, specify in the ID field the identifier of the Host you want to access. Now the Client, when connecting, will always use the Internet-ID module.
To use the Internet-ID for an existing connection, in its properties (section “Basic Settings”), specify the desired ID and check the box to the left of it.
To connect directly and disable the use of the Internet-ID mechanism, simply uncheck the box to the left of the ID in the connection settings.
Mini Internet-ID server.
System administrators have the opportunity to deploy their own corporate Internet-ID server, so as not to depend on the servers of the TektonIT company. Find out more about the Mini Internet-ID server here.
Foreword
Since our site is designed for average users, there is no mistake inside the team. There were some disagreements regarding the usefulness of this article. Usually, such material is served for more experienced users who at least have a good knowledge of Windows.
On the other hand. Where to go to a novice user who only remotely represents what RDP, TCP, UDP? But really want to know? Again, does the average user need this? Maybe one simple program is enough for him?
Explain in one article what is remote access to a computer via the Internet, but so as not to frighten the visitor.
We decided on an experiment. Talk about the difficult, as affordable as possible. We will focus on your comments.
What is this article about?
This article will tell you about two types of remote connection, briefly talk about what is ID. Will tell about programs Remote access and Remote desktop. We will also try to configure our computer in order to gain remote access to it without using third-party programs. The complex terms in the article are highlighted in brown, and provided with explanations in the form of tooltips.
The concept of remote access
Remote access to a computer via the Internet is the means of the operating system, or a third-party program that allows you to get visual or file access to a computer located at a remote distance, but connected to the Internet.
How is the right computer on the Internet recognized?
Conventionally, all remote access programs, by type of connection, can be divided into two groups:
- Using ID
- Using IP addresses and domain names
Remote Access Programs Using ID
Of great interest are programs using ID (unique identificator). Production method ID something like this: when a remote access program is launched on the computer to which you are connecting, it sends a request to its server through which it will connect.
The request contains data that identifies the computer, for example, the serial number of the hard drive, MAC address, etc.
Having received this data, the server generates for the computer unique identification number. ID. This number is assigned to the computer. In the screenshot below, it is highlighted in red.
TeamViewer Interface
Knowing this identification number and password. You can connect to a computer from anywhere in the world with this ID.
It remains unchanged until the equipment is replaced or the OS is reinstalled.
So the use of such programs is very convenient. When changing your Internet provider, city, or even country, at your computer ID Will not change.
Lack of programs using ID one. They are paid or shareware. Condition. You must not use the program for commercial purposes.
Example programs using ID. TeamViewer, Ammy Admin (Ammyy cannot be downloaded by the Chrome and Firefox browsers. Use another browser, for example Internet Explorer, Edge, Opera, Yandex.Browser.
But the list is not limited to these two. They are simply the most popular and always heard by users.
We will not spend much time on these programs, as their interface is simple, and allows you to learn the program in 5-10 minutes. In the future, we may consider each of them.
You will have no problems with these programs. Use your health without abuse. If TeamViewer will connect to a large number ID. Sooner or later, the communication session will be limited to five minutes.
Remote access programs using an IP address or domain name
With this category, things are a little more complicated. They need a static ip address or domain name. Connection by IP address, This is a classic type of connection. It does not provide such flexibility in the location of the computer and is most often used in the “office space”.
In order to use it, you must do the following.
Connect a fixed IP address or domain.
You need to connect an additional service with your provider. [simple_tooltip content = ’IP address that does not change when the router or modem is rebooted’] Fixed ip address [/ simple_tooltip]. This service is provided by many providers, including mobile ones. This service will assign an external IP address of the format 123.123.123.123 to your home network
It is this address that will allow you to find your computer from outside.
An alternative to a fixed ip-address is the service Dyndns. Upon registration, you will be given an individual domain, for example:
Neoshibka.Dyn.com
Next, you simply install on your computer a program that, when turned on, will track your current ip-address and send it to the server Dyndns, which in turn will match your current [simple_tooltip content = ’” address, which changes with every disconnection (reboot of the modem, router). ‘] dynamic ip address [/ simple_tooltip], with the address yourlogin.Dyn.com
Thus, wherever you are, whatever provider you use, no matter how often your IP address. The address of your computer. Yourlogin.Dyn.com
We don’t take it for granted, but getting a fixed IP address from the provider is somewhat simpler and cheaper than using Dyndns. For example, at the time of this writing, the cost of a dedicated IP address was only 20 rubles. / month
Opening the port to the target is a remote computer.
Even now, knowing our ip address or assigned to us Dyndns domain, we can hardly connect to the computer. The firewall will not let us through. Most likely the port 3389 used by the program Remote desktop which we tame in this article will be closed. For everything to work as it should. We will have to open it and redirect it to the desired computer on the network.
Complicated? Not at all. Let’s try to understand in practice.
Remote access to a computer via the Internet using Remote Desktop
So, the first what we did was get a fixed ip-address from our provider. Remember, write, draw it.
Second. Let us find out [simple_tooltip content = ’the Address assigned to the network adapter, in the“ Network and Sharing Center ”‘] the intranet ip address [/ simple_tooltip] of our computer. To do this, go along the following path: Network and Sharing Center = Local Area Connection = Intelligence As can be seen in the screenshot, the address of our computer on the network 192.168.1.102
Third point will be the opening of the port 3389 to the above address. To do this, let’s go to the router. In our case, this ADSL modem TP-LINK. We will show everything with his example. There is nothing to be done, but instructions cannot be dispensed with if you do not know how to configure the modem yourself.
In our case, we go through Google chrome by the address 192.168.1.1 and under the combination admin / admin. We get to the information page.
Go to Advanced Setup = NAT = Virtual servers and press the button (add).
Here you can choose ready-made services or create your own.
We will create our own and name it. Udalenka, but the name can be anything. We register the local address of the computer, the one that was spied earlier. In the table, register the port everywhere 3389 and select the protocol TCP / UDP. We do all this based on a standard Windows application Remote desktop. For other programs, the ports may be different. A good list of applications and the ports they use is given here. (What we learn may come in handy even for games).
If for example you want to use not Remote desktop, and advanced Radmin, then it will have to register another port: 4899.
Click the button to save.
Paragraph fourth, we will run on the computer we are going to manage. Terminal server service. There is something to clarify.
We do all this for the purpose of acquaintance and in order to learn the principles of the remote access to a computer via the Internet.
So, to run on a computer Terminal server service. In Windows XP, this was done simply. Went to Administration. Services and Applications. Services found it and just turned it on. This made it possible for one user to connect to a computer. In this case, the user who was sitting locally disconnected.
In Windows 10, we need to do a little different. We need a special patch. You can download it from here. This patch will run on the system Windows 10 terminal service.
Unzip the downloaded file to any place. For example on Desktop. Run as Administrator file install.Bat
A black command line window with the following contents will report a successful result:
Fifth with the item we will set a password for our user, and also add it to the group Remote Desktop Users.
To do this, on the icon [simple_tooltip content = ’My computer for XP, This computer for Windows 10 ‘] A computer [/ simple_tooltip] and right-click to select Control.
In the window that opens, in the left part, we need to expand the list Local users and groups, highlight subparagraph Users.
In the list of users, you need to find yourself and right-click Set a password..
Enter the password twice, press and the system will confirm that the password is set.
Now we need to add our user to the group Remote Desktop Users.
To do this:
Right click on user. Properties.
In the window that opens, go to the tab Group membership and click on the button
Next, do everything in the order shown in the screenshot:
As a result of the work done. Remote Desktop Users should appear in the general list of groups the user belongs to.
Check if we were able to access the computer remotely via the Internet using Remote desktop.
We leave to another computer, go to START menu = All programs = Standard and run the program “Remote Desktop Connection”.
Enter the IP address assigned to us earlier by the provider in the window that appears, click the button.
If everything we did before, we did right, then they will ask us almost immediately Name and Password user on Remote car. Enter them and do not forget to check the box to remember the credentials.
And the last “security touch” will be checking the certificate of the Remote Machine. Here, too, you need to agree with everything. And also tick.
That’s all. If everything works as it should, you can climb in the settings of the Remote Desktop program. Here you can enable / disable sound, change image quality, connect [simple_tooltip content = ’Printers, flash drives, disks, etc.’] local resources [/ simple_tooltip] to the remote machine.